Is that allowed? Authentication and authorization in Model Context Protocol
Learn how to protect MCP servers from unauthorized access and how authentication of MCP clients to MCP servers works.
 Technology
Technology
In this episode, Thomas Betts and Sam McAfee discuss how AI hype is reshaping organizational behavior, why many companies struggle with experimentation, and how unclear decision structures create fric...
 Technology
Technology
This week's Java roundup for March 2nd, 2026, features news highlighting: the GA release of Apache Solr 10; point releases of LangChain4j, JobRunr, Multik and Gradle; maintenance releases of Grails an...
 Technology
Technology
Patrick Debois discusses the evolution of software engineering in the age of AI. He shares four key patterns: transitioning from producer to manager, focusing on intent over implementation through spe...
 Sports
Sports
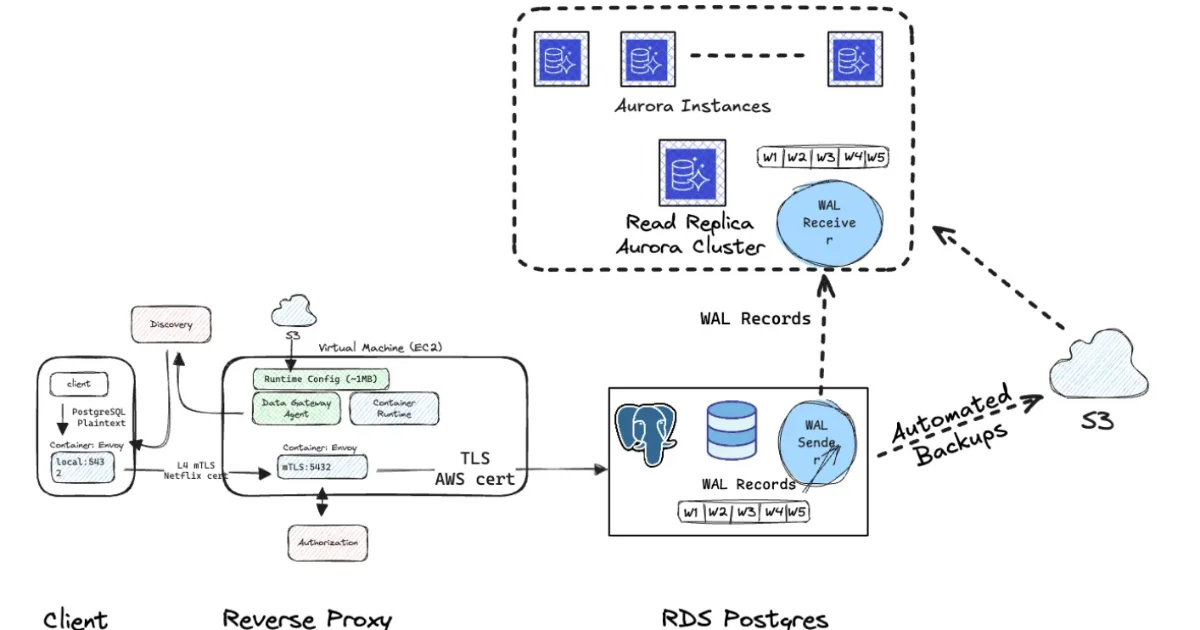
Netflix engineers describe an internal automation platform that migrates nearly 400 RDS PostgreSQL clusters to Aurora, reducing downtime and operational risk. The platform coordinates replication, CDC...
 Technology
Technology
Cloudflare released vinext, an experimental Next.js reimplementation built on Vite by one engineer, with AI guidance over one week, for $1,100. Early benchmarks show 4.4x faster builds, but Cloudflare...
 Technology
Technology
Artificial intelligence is rapidly transforming how software vulnerabilities are detected, but questions about who governs the risks AI exposes, and how those risks are acted on, are becoming increasi...
 Technology
Technology
After the Datadog Agent grew from 428 MiB to 1.22 GiB over a period of 5 years, Datadog engineers set out to reduce its binary size. They discovered that most Go binary bloat comes from hidden depende...
 Technology
Technology
Uno Platform 6.5 introduces Antigravity AI agent support, allowing agents to verify app behavior at runtime. Hot Design now launches by default with a redesigned toolbar and new scope selector. The re...
 Technology
Technology
AI-powered bot hackerbot-claw exploited GitHub Actions workflows across Microsoft, DataDog, and CNCF projects over 7 days using 5 attack techniques. Bot achieved RCE in 5 of 7 targets, stole GitHub to...
 Technology
Technology
Every MCP tutorial I've found so far has followed the same basic script: build a server, point Claude Desktop at it, screenshot the chat window, done. This is fine if you want a demo. But it's not fin
 Technology
Technology
Finding the top K items in a dataset pops up everywhere: from highlighting the hottest posts in a social feed, to detecting the largest transactions in a financial system, or spotting the heaviest use
 Technology
Technology
Ever wondered how Gmail knows that an email promising you $10 million is spam? Or how it catches those "You've won a free iPhone!" messages before they reach your inbox? In this tutorial, you'll build
AI agents are quickly becoming autonomous digital actors embedded in enterprise workflows. Unfortunately, as organizations scale from dozens to hundreds of agents across clouds, platforms, and busines...
Unpack the critical role of privacy within the five SOC 2 trust services criteria (TSC) and how organizations can leverage compliance to build trust and resilience in a data-driven world. In this post...
India’s banking system is undergoing a critical shift in how digital trust is established. With the rise of phishing, impersonation fraud, and look-alike banking websites, the Reserve Bank of India (R...